Identity and Access Management (IAM) is no longer just a layer of security—it has evolved into a critical business enabler. From onboarding employees efficiently to ensuring regulatory compliance and enabling secure digital transformation, IAM sits at the heart of modern enterprise operations.
Despite its importance, many organizations struggle with a persistent, often underestimated challenge: slow IAM deployment.
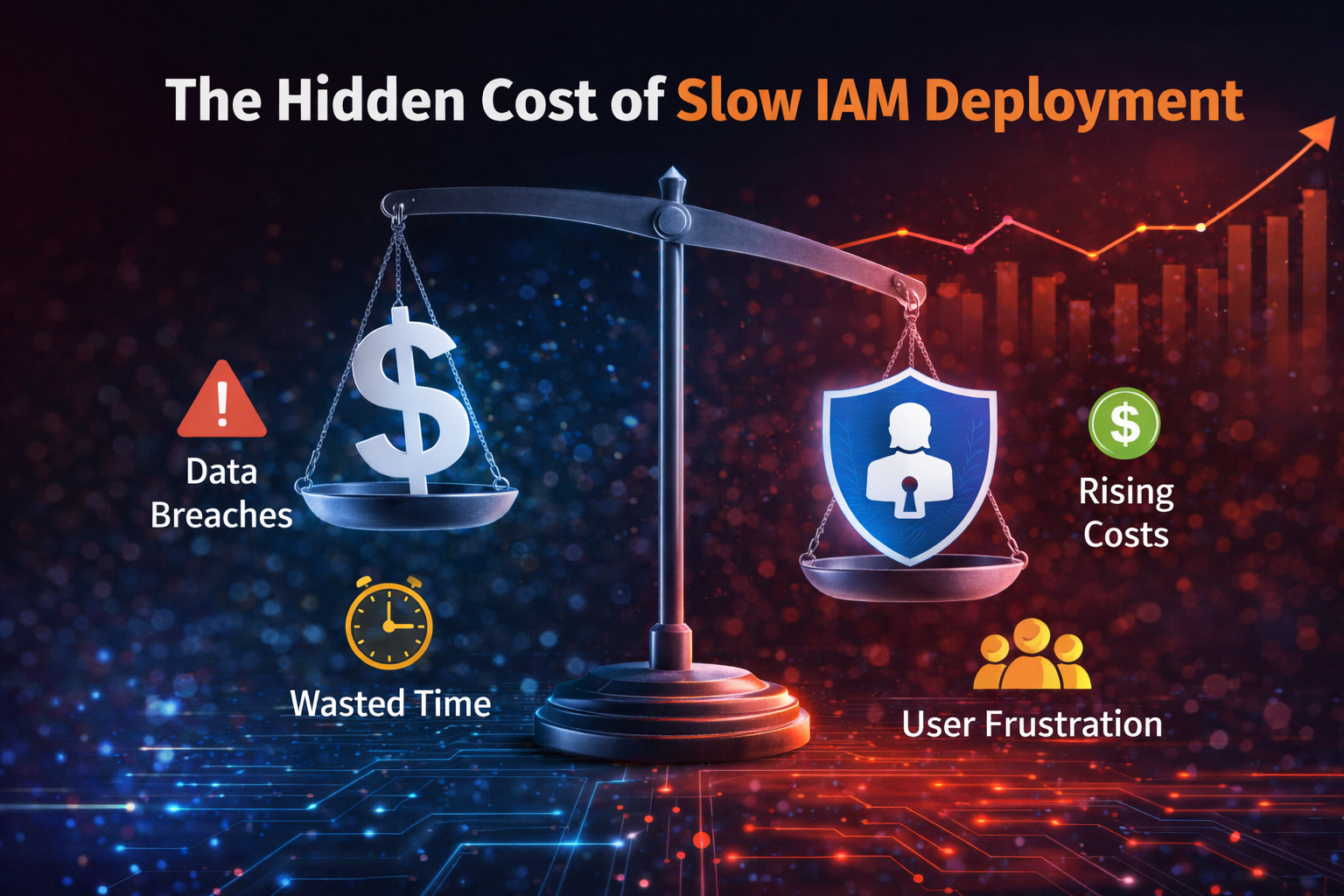
At first glance, implementation delays may appear manageable—just a few weeks added to timelines or minor integration setbacks. However, as these delays accumulate, they begin to create ripple effects across the organization. What starts as a technical delay gradually becomes a business problem, affecting security, productivity, compliance, and overall performance.
To truly understand how to avoid these outcomes, it’s important to first recognize the root causes behind why IAM Projects fail and how organizations can implement IAM successfully with the right strategy.
Slow IAM deployment is not just about missed deadlines—it often reflects deeper inefficiencies in an organization’s technology and processes.
It can manifest in several ways: delayed employee onboarding, prolonged application integrations, heavy reliance on manual provisioning, and extended implementation cycles that far exceed initial expectations. These inefficiencies are typically rooted in legacy systems, a lack of integration planning, and the absence of a structured implementation roadmap.
Organizations that take the time to build a clear IAM roadmap and prioritize early integration are better positioned to avoid these delays and achieve a more streamlined implementation journey.
One of the most immediate and critical consequences of slow IAM deployment is the increased exposure to security risks. When IAM systems are only partially implemented, users often retain access privileges longer than necessary, and manual errors become more frequent.
Delayed deprovisioning and lack of centralized control create gaps that can be exploited, increasing the likelihood of unauthorized access or data breaches. Over time, these vulnerabilities can have serious financial and reputational consequences for the organization.
Beyond security, slow IAM directly impacts the day-to-day productivity of employees and teams. When access to applications and systems is delayed, employees are unable to perform their roles efficiently.
IT teams, on the other hand, are often burdened with repetitive manual tasks such as provisioning and access approvals. This not only slows down business workflows but also diverts valuable resources away from more strategic initiatives.
The result is a workplace environment where inefficiencies become normalized, and both employees and IT teams experience growing frustration.
IAM is often viewed as a long-term investment in security and efficiency. However, when deployment is slow, it begins to behave more like an ongoing operational expense.
Delays lead to extended development efforts, continuous rework, and increased reliance on manual processes. Organizations may find themselves allocating additional resources to maintain incomplete systems, driving up costs without delivering proportional value.
In such scenarios, the true cost of IAM is not in its implementation—but in its delay.
IAM plays a central role in maintaining regulatory compliance and ensuring audit readiness. When implementation is delayed, organizations struggle to establish complete audit trails, enforce access governance policies, and generate consistent reports.
These gaps can lead to compliance failures, especially in highly regulated industries where visibility and accountability are critical. The longer the IAM deployment is delayed, the more difficult it becomes to meet regulatory requirements and avoid potential penalties.
IAM is a foundational component for broader digital transformation efforts, including cloud adoption, automation, and Zero Trust security models.
When IAM deployment is slow, it creates a bottleneck that impacts these initiatives. Organizations may find themselves unable to move forward with modernization efforts because the underlying identity infrastructure is not yet mature.
In this way, IAM delays do not just affect security—they slow down the organization’s ability to innovate and compete in a digital-first world.
In today’s fast-paced work environment, users expect seamless and immediate access to the tools they need. Slow IAM processes, however, often lead to login issues, access delays, and inconsistent user experiences.
When employees are unable to access systems efficiently, they may turn to unauthorized tools or workarounds—leading to the rise of shadow IT. This not only undermines security but also creates additional governance challenges for the organization.
A major contributor to slow IAM deployment is the difficulty of integrating with legacy systems. Many enterprises operate with outdated platforms that lack modern APIs or standardized integration capabilities.
