In today’s digital enterprise, managing who has access to what is no longer just an IT task—it’s a critical business priority. With organizations operating across cloud platforms, legacy systems, SaaS applications, and remote work environments, Identity and Access Management (IAM) has become the backbone of enterprise security.
However, many organizations struggle with fragmented identity systems, manual provisioning, compliance risks, and delayed application onboarding. This is where a well-structured IAM roadmap becomes essential.
An effective IAM implementation of roadmap helps enterprises transition from reactive access management to a strategic identity-centric security framework. In this guide, we’ll walk through a step-by-step IAM strategy that enterprises can follow to successfully implement and scale IAM across their organization.
Many organizations jump into IAM projects by selecting tools before defining their strategy. This often leads to delays, integration issues, and poor user adoption.
A well-defined IAM roadmap helps enterprises:
Most importantly, it provides a structured IAM implementation roadmap that reduces complexity and ensures long-term scalability.
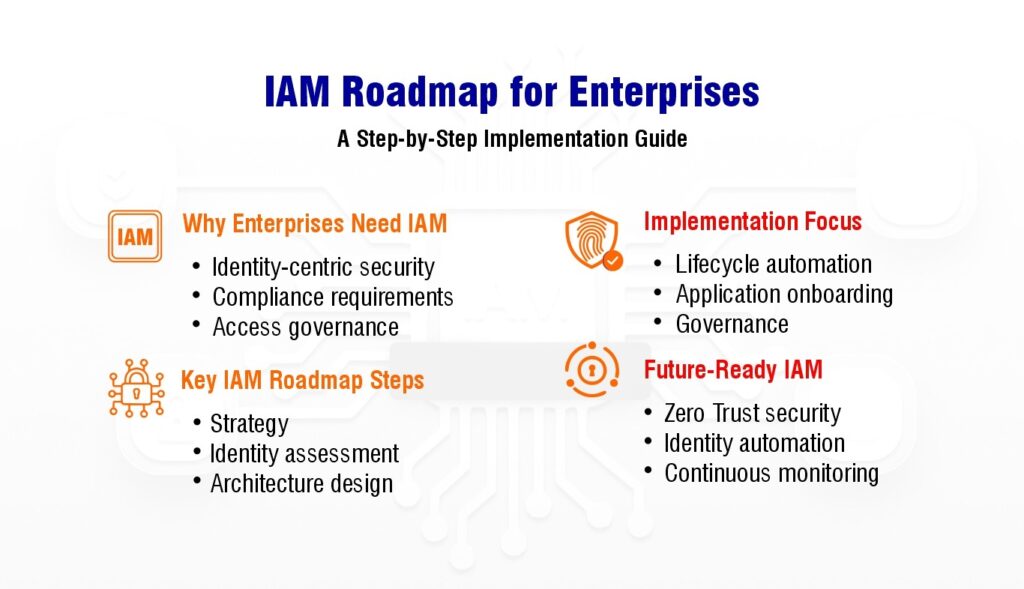
The first step in building an effective IAM strategy is to understand the organization’s security goals and operational needs.
Important factors to consider:
During this stage, enterprises should involve stakeholders from IT, security, compliance, HR, and business units to ensure the IAM roadmap aligns with broader organizational priorities.
A well-defined IAM strategy forms the foundation of a successful IAM implementation roadmap.
Before implementing IAM, organizations must evaluate their existing identity infrastructure.
This assessment typically includes:
Enterprises often discover fragmented identity systems and inconsistent access policies during this phase.
Understanding these gaps helps define the scope of the IAM roadmap and highlights integration challenges early in the implementation process.
Not every application needs to be onboarded into IAM at once. A phased approach ensures smoother implementation and reduces operational risks.
Priorities for organizations should be:
This prioritization becomes a key component of the IAM implementation roadmap, allowing enterprises to achieve quick wins while gradually expanding identity governance coverage.
Once priorities are established, the next step is designing a scalable IAM architecture.
A typical enterprise IAM architecture includes:
Organizations must also plan how to integrate legacy systems, SaaS platforms, and custom applications into the IAM framework.
This is where modern integration solutions—such as identity gateways or automation layers—can significantly simplify application onboarding and reduce integration complexity.
One of the biggest benefits of IAM is automated identity lifecycle management.
This includes managing the entire user journey:
Automating these processes ensures that users receive the right access at the right time while preventing unauthorized access after role changes or employee departures.
A strong lifecycle management strategy is a cornerstone of an effective IAM roadmap.
Regulatory frameworks and internal security policies require organizations to maintain strict access controls.
IAM enables enterprises to enforce:
These capabilities help organizations strengthen governance while simplifying compliance with industry standards.
By integrating governance into the IAM implementation roadmap, enterprises can ensure that identity security aligns with regulatory requirements.
One of the biggest challenges in enterprise IAM projects is integrating diverse applications.
Many legacy systems lack modern APIs or identity connectors, making integration complex and time-consuming.
To address this challenge, organizations can leverage integration platforms that support:
These technologies accelerate application integration and reduce the operational overhead of IAM deployments.
IAM is not a one-time implementation—it’s an ongoing process.
Once the IAM system is deployed, organizations should continuously monitor:
Regular reviews help refine the IAM strategy and ensure the IAM roadmap evolves with business needs, new technologies, and emerging security threats.
Even with a well-planned IAM implementation roadmap, enterprises often face challenges such as:
Addressing these challenges requires both strong IAM governance and flexible integration capabilities that simplify identity automation across enterprise systems.
Tired of IAM Delays Slowing You Down?
Accelerate deployment with a smarter integration strategy.
👉 Schedule a Demo
As organizations adopt cloud platforms, remote work models, and digital ecosystems, identity becomes the new security perimeter.
A future-ready IAM strategy should focus on:
By following a structured IAM roadmap, enterprises can build a secure, scalable identity framework that supports digital transformation while protecting critical business assets.
Implementing IAM is not just about deploying technology—it’s about creating a strategic identity framework that aligns security, compliance, and business operations.
