Identity and Access Management (IAM) is a critical pillar of modern enterprise security and digital transformation. It ensures the right users have the right access at the right time—while maintaining compliance and minimizing risk.
However, despite increasing investments in IAM implementation, many organizations struggle to achieve success.
Projects are delayed. Integration challenges arise. Costs escalate. And in some cases, implementations are abandoned altogether.
So, why do IAM projects fail?
This blog explores the most common IAM challenges and highlights the key reasons enterprises struggle with identity governance and access management implementation.
If you're planning your IAM journey, start with a structured approach like building an enterprise IAM roadmap to avoid common problems.
At a surface level, IAM implementation appears straightforward—connect applications, define access policies, and manage identities.
IAM is deeply connected to:
This makes IAM deployment complexity one of the biggest challenges organizations face.
For example, a simple access request may involve multiple systems, approvals, and compliance checks—making even basic workflows complex to manage.
1. Legacy System Integration Challenges
One of the biggest barriers to successful IAM implementation is integrating with legacy systems.
Many enterprises rely on outdated platforms and custom-built applications that lack APIs or modern connectors. This creates major IAM integration challenges.
For instance, a large enterprise running an older ERP system may require custom development just to enable identity synchronization. This increases implementation time and introduces long-term maintenance risks.
As a result, integration becomes the biggest bottleneck in enterprise IAM deployment.
2. Underestimating IAM Implementation Complexity
IAM is not just a technical solution—it is a business transformation initiative involving multiple stakeholders.
Organizations often underestimate:
This leads to poor planning, frequent scope changes, and delays in IAM project execution.
3. Over-Reliance on Custom Development
To overcome integration gaps, organizations often rely heavily on custom coding.
While this may solve short-term issues, it creates long-term challenges in IAM scalability and maintenance.
For example, building custom connectors for internal applications can make future upgrades difficult and increase dependency on specific developers.
This approach slows down innovation and increases operational risk.
4. Lack of a Clear IAM Strategy
Without a well-defined IAM strategy and roadmap, projects quickly lose direction.
Organizations often fail to define:
This results in fragmented execution and poor outcomes in identity governance implementation.
5. Poor Data Quality and Identity Governance Issues
IAM systems rely heavily on accurate identity data.
However, many organizations struggle with:
This leads to incorrect provisioning, security risks, and compliance failures.
Improving identity data management is critical for successful IAM deployment.
6. Compliance and Audit Challenges in IAM
IAM plays a central role in regulatory compliance and access governance.
Without proper planning, organizations face:
This becomes especially critical in industries with strict compliance requirements.
7. Resistance to Change in IAM Adoption
IAM implementation often requires organizational change.
New workflows, approval systems, and access controls can create resistance among employees.
Without proper IAM change management strategies, adoption becomes a major barrier to success.
IAM failures are not just technical—they are strategic.
They stem from:
Understanding these issues is the first step toward building a successful enterprise IAM strategy.
Facing IAM Implementation Challenges?
Struggling with IAM integration complexity, slow deployment, or legacy system issues?
Discover how organizations are accelerating IAM implementation using modern, scalable approaches.
#IdentityAccessManagement #IAM #CyberSecurity #DigitalTransformation #IAMImplementation #LegacySystems #EnterpriseIT #ZeroTrust #AccessManagement #BookADemo
In today’s hyper-connected enterprise ecosystem, identity has quietly become the new control plane for security.
Organizations no longer operate within a single application environment. Instead, they rely on a constantly expanding mix of cloud platforms, SaaS tools, legacy systems, APIs, partner portals, and hybrid infrastructures. While this digital expansion has accelerated innovation, it has also introduced a growing identity challenge — one that traditional Identity and Access Management (IAM) systems were never designed to handle.
According to recent Gartner IAM roadmap insights, the future of enterprise security lies not in deploying more IAM tools, but in integrating identity across the entire digital landscape. This is where the concept of Identity Integration Platforms begins to reshape how modern organizations approach IAM.
Over the past decade, enterprises have adopted multiple identity solutions to address different needs:
While each of these tools solves a specific problem, they often operate in silos — resulting in fragmented identity governance across the enterprise.
This leads to:
In industries like aviation and gaming — where Bridgesoft IAM solutions are increasingly being deployed — managing identity across legacy reservation systems, operational platforms, third-party APIs, and cloud-native applications has become particularly complex.
The traditional IAM approach simply doesn’t scale in these environments.
Gartner IAM roadmap now emphasizes a shift from standalone identity management tools toward integrated identity ecosystems that can unify authentication, authorization, and governance across diverse technology stacks.
Rather than managing identity at the application level, organizations are being encouraged to treat identity as an integration layer — connecting:
This shift reflects a broader move toward identity-first security models, where access decisions are made dynamically based on context, risk signals, and policy orchestration across platforms.
Identity Integration Platforms are designed to bridge the gap between fragmented IAM deployments and modern enterprise infrastructure.
Instead of replacing existing IAM investments, these platforms enable organizations to:
This approach allows enterprises to unify identity operations without disrupting mission- critical systems, which are a crucial requirement for sectors that depend on continuous availability and compliance.
As enterprises continue their digital transformation journeys, identity is becoming deeply embedded in every business transaction — from employee onboarding and customer logins to partner integrations and machine-to-machine communications.
Managing these identities in isolation is no longer sustainable.
By aligning with Gartner IAM trends and adopting Identity Integration Platforms, organizations can:
The future of IAM is no longer about managing identities within applications — it's about integrating identity across ecosystems.
Identity Integration Platforms represent the next phase of the IAM evolution, enabling enterprises to move from fragmented identity management toward a unified, policy-driven identity fabric.
As organizations revisit their IAM roadmap considering Gartner’s strategic direction, investing in identity integration may well become the foundation for scalable, secure digital growth.
Gartner, Develop an IAM Program Roadmap to Deliver Business Value, Steve Wessels, Rebecca Archambault, Brian Guthrie, 2 September 2025.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
In today’s digital enterprise, managing who has access to what is no longer just an IT task—it’s a critical business priority. With organizations operating across cloud platforms, legacy systems, SaaS applications, and remote work environments, Identity and Access Management (IAM) has become the backbone of enterprise security.
However, many organizations struggle with fragmented identity systems, manual provisioning, compliance risks, and delayed application onboarding. This is where a well-structured IAM roadmap becomes essential.
An effective IAM implementation of roadmap helps enterprises transition from reactive access management to a strategic identity-centric security framework. In this guide, we’ll walk through a step-by-step IAM strategy that enterprises can follow to successfully implement and scale IAM across their organization.
Many organizations jump into IAM projects by selecting tools before defining their strategy. This often leads to delays, integration issues, and poor user adoption.
A well-defined IAM roadmap helps enterprises:
Most importantly, it provides a structured IAM implementation roadmap that reduces complexity and ensures long-term scalability.
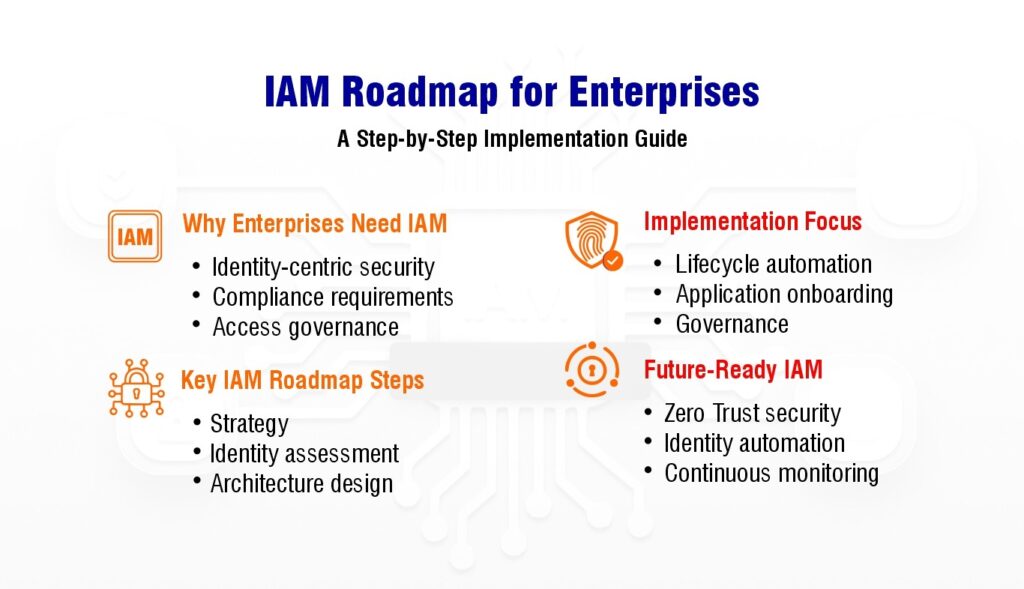
The first step in building an effective IAM strategy is to understand the organization’s security goals and operational needs.
Important factors to consider:
During this stage, enterprises should involve stakeholders from IT, security, compliance, HR, and business units to ensure the IAM roadmap aligns with broader organizational priorities.
A well-defined IAM strategy forms the foundation of a successful IAM implementation roadmap.
Before implementing IAM, organizations must evaluate their existing identity infrastructure.
This assessment typically includes:
Enterprises often discover fragmented identity systems and inconsistent access policies during this phase.
Understanding these gaps helps define the scope of the IAM roadmap and highlights integration challenges early in the implementation process.
Not every application needs to be onboarded into IAM at once. A phased approach ensures smoother implementation and reduces operational risks.
Priorities for organizations should be:
This prioritization becomes a key component of the IAM implementation roadmap, allowing enterprises to achieve quick wins while gradually expanding identity governance coverage.
Once priorities are established, the next step is designing a scalable IAM architecture.
A typical enterprise IAM architecture includes:
Organizations must also plan how to integrate legacy systems, SaaS platforms, and custom applications into the IAM framework.
This is where modern integration solutions—such as identity gateways or automation layers—can significantly simplify application onboarding and reduce integration complexity.
One of the biggest benefits of IAM is automated identity lifecycle management.
This includes managing the entire user journey:
Automating these processes ensures that users receive the right access at the right time while preventing unauthorized access after role changes or employee departures.
A strong lifecycle management strategy is a cornerstone of an effective IAM roadmap.
Regulatory frameworks and internal security policies require organizations to maintain strict access controls.
IAM enables enterprises to enforce:
These capabilities help organizations strengthen governance while simplifying compliance with industry standards.
By integrating governance into the IAM implementation roadmap, enterprises can ensure that identity security aligns with regulatory requirements.
One of the biggest challenges in enterprise IAM projects is integrating diverse applications.
Many legacy systems lack modern APIs or identity connectors, making integration complex and time-consuming.
To address this challenge, organizations can leverage integration platforms that support:
These technologies accelerate application integration and reduce the operational overhead of IAM deployments.
IAM is not a one-time implementation—it’s an ongoing process.
Once the IAM system is deployed, organizations should continuously monitor:
Regular reviews help refine the IAM strategy and ensure the IAM roadmap evolves with business needs, new technologies, and emerging security threats.
Even with a well-planned IAM implementation roadmap, enterprises often face challenges such as:
Addressing these challenges requires both strong IAM governance and flexible integration capabilities that simplify identity automation across enterprise systems.
Tired of IAM Delays Slowing You Down?
Accelerate deployment with a smarter integration strategy.
👉 Schedule a Demo
As organizations adopt cloud platforms, remote work models, and digital ecosystems, identity becomes the new security perimeter.
A future-ready IAM strategy should focus on:
By following a structured IAM roadmap, enterprises can build a secure, scalable identity framework that supports digital transformation while protecting critical business assets.
Implementing IAM is not just about deploying technology—it’s about creating a strategic identity framework that aligns security, compliance, and business operations.
Introduction
As digital enterprises continue to expand their technology ecosystems across cloud, on-premises, and hybrid environments, managing user identities and access is becoming an increasingly important component of enterprise security strategy.
According to industry reports, organizations implementing a structured Identity and Access Management (IAM) strategy are significantly better positioned to reduce insider threats, improve audit readiness, and accelerate application onboarding.
This is where developing a structured IAM Roadmap can provide strategic value.
Why Enterprises Need an IAM Roadmap
Many organizations deploy IAM tools without establishing a long-term identity governance strategy. As a result, they often encounter:
An IAM Roadmap can help enterprises transition from fragmented identity management practices toward a more centralized and automated identity lifecycle framework.
Key Components of an Effective IAM Roadmap
To build a scalable IAM program, enterprises should focus on the following phases:
1. Identity Lifecycle Management
An IAM Roadmap should consider addressing the complete Joiner-Mover-Leaver (JML) process to ensure:
This reduces the risk of unauthorized access due to inactive or over-privileged accounts.
2. Access Governance and Certification
Periodic access reviews and certifications help enterprises:
Governance frameworks can contribute to improving oversight of identity-related risks across enterprise systems.
3. Application Integration Strategy
Integrating legacy and business-critical applications into modern IAM platforms remains a common implementation challenge.
Traditional integration methods rely heavily on custom connectors — increasing deployment time and operational overhead.
Modern IAM Roadmaps should include an Application Onboarding Strategy that supports:
This approach enables faster integration and improved identity data exchange across environments.
Turn IAM Challenges into Quick Wins
Drive faster implementation with minimal friction.
👉 Request Your Demo
4. Automated Provisioning Framework
Provisioning automation helps enterprises:
Automated identity provisioning is essential for maintaining security posture in rapidly evolving IT environments.
IAM Integration: The Missing Link in Most Roadmaps
Despite investing in IAM technologies, many organizations struggle with onboarding applications into identity platforms.
A successful IAM Roadmap must incorporate an integration layer that bridges:
This integration capability allows organizations to standardize identity operations such as:
across both modern and legacy systems.
Aligning IAM Strategy with Business Growth
An enterprise IAM Roadmap may also support broader business initiatives by enabling:
With an appropriate roadmap in place, organizations may improve identity visibility while reducing operational dependencies.
Conclusion
As highlighted in multiple enterprise security studies referenced by Gartner, Identity and Access Management is no longer just an IT function — it is a business enabler.
Developing a future-ready IAM Roadmap allows enterprises to:
A strategic IAM framework ensures that organizations can securely manage identities across evolving digital ecosystems while maintaining agility and operational efficiency.
Gartner, Develop an IAM Program Roadmap to Deliver Business Value, Steve Wessels, Rebecca Archambault, Brian Guthrie, 2 September 2025.
GARTNER is a registered trademark and service mark of Gartner, Inc. and/or its affiliates in the U.S. and internationally and is used herein with permission. All rights reserved.
The term “Zero Trust” has become a mainstay in cybersecurity conversations, yet it’s often misunderstood or misapplied. At its core, Zero Trust is a security model built on the principle of “never trust, always verify.” It assumes that threats can exist both outside and inside the network and that no user or system should be inherently trusted.
This approach has profound implications for how organizations manage identity and access. Identity is no longer just one piece of a broader strategy it’s the foundation. While Zero Trust can be an ambitious undertaking, practical, identity-centric strategies can help organizations make meaningful progress without boiling the ocean.
In a Zero Trust architecture, identity becomes the most critical control point. Every access request must be authenticated, authorized, and continuously validated based not just on credentials, but on context such as device health, user behaviour, location, and risk level.

This shifts the focus from perimeter-based defences to identity-based access control, where policies govern how and when users can access resources. Implementing adaptive access controls, integrating multifactor authentication (MFA), and leveraging identity analytics are key steps toward enforcing Zero Trust principles. These measures allow organizations to dynamically assess risk and respond in real time, rather than relying on static roles or outdated permissions.
While the concept of Zero Trust is widely accepted, its implementation often falters due to scope and complexity. Many organizations attempt to implement it all at once, leading to resource strain and diminished momentum. A more pragmatic approach begins with prioritizing high-risk assets and users such as privileged accounts, critical applications, or third-party access.
Organizations can start by establishing strong identity foundations: centralizing identity data, enabling single sign-on (SSO), enforcing least privilege access, and automating provisioning and deprovisioning processes. From there, layered policies can be introduced to enforce conditional access based on contextual signals. The key is to take an iterative approach assessing risks, identifying gaps, and incrementally introducing controls that align with business operations.
One of the common pitfalls in Zero Trust initiatives is failing to align technical controls with business outcomes. Identity strategies must not only protect systems but also support operational agility. For example, sales teams require quick access to CRM platforms while traveling, and developers may need temporary access to production environments. Applying Zero Trust doesn’t mean limiting productivity it means enabling it securely.
Cross-functional alignment is essential. Security leaders must work with business stakeholders to understand workflows, pain points, and regulatory requirements. Zero Trust policies should reflect real-world use cases and strike a balance between protection and usability. When executed properly, Zero Trust becomes an enabler of innovation, not an obstacle.
Ready to Accelerate Your IAM Journey ?
Move from planning to execution—faster and smoother.
👉 Book a Demo
Zero Trust is not a product or a one-time project it’s a long-term security mindset. It requires continuous validation, adaptive controls, and identity as a strategic anchor. Organizations that begin with a clear understanding of their risk landscape and take focused steps toward maturity will see measurable gains in both security posture and operational efficiency. Ultimately, identity is where Zero Trust begins and where its success is measured. By adopting identity-first strategies that are grounded in business context, organizations can turn Zero Trust from a buzzword into a blueprint for resilient security.
Digital transformation has reshaped how businesses operate, and with it, the concept of identity has evolved. No longer limited to human users, today’s enterprises rely on machine identities non-human entities that authenticate, communicate, and execute critical workflows. From cloud workloads and DevOps pipelines to IoT devices and AI driven automation, machine identities now outnumber human users in many organizations.
Yet, despite their growing importance, these identities often remain unmanaged, overprivileged, and vulnerable making them prime targets for cyberattacks.
What Are Machine Identities?
Machine identities are digital credentials that enable secure authentication and communication for non-human entities. These include:
Unlike human users, machine identities operate silently in the background often with persistent access, excessive privileges, and weak rotation policies. This makes them a goldmine for attackers looking to escalate privileges or move laterally across networks.
Why Machine Identity Governance is Critical Neglecting machine identities leads to security blind spots and compliance risks. High profile breaches often stem from exposed API keys, misconfigured service accounts, or hardcoded credentials. In cloud native environments, where workloads scale dynamically, the risks multiply.
Key challenges include:
Credential sprawl – Uncontrolled accumulation of machine identities with no clear ownership
Privilege creep – Over permissioned service accounts increasing attack surfaces
Manual mismanagement – Secrets stored in plaintext, hardcoded scripts, or shared carelessly
Audit gaps – No visibility into who created an identity, what it accesses, or if it’s still needed
Security teams can’t protect what they can’t see. Without governance, machine identities become invisible and exploitable.
The Expanding Attack Surface
Machine identities now permeate every layer of IT:
Attackers exploit these weak points through credential harvesting, token theft, and privilege escalation. Worse, breaches often go undetected for months because machine activity isn’t logged or monitored effectively.
How to Secure Machine Identities: A Lifecycle Approach
To mitigate risks, organizations must adopt automated, policy driven governance for non-human identities. Here’s how:
1. Discovery & Inventory
Scan systems, code, and cloud environments to detect unmanaged credentials.
2. Classification & Ownership
Tag identities by criticality and assign ownership to ensure accountability.
3. Least Privilege Access
Enforce role based policies grant only necessary permissions.
4. Automated Secret Management
Encrypt & rotate credentials eliminate hardcoded secrets.
5. Continuous Monitoring
Log machine activity and detect anomalies (e.g., unusual API calls).
6. Timely Decommissioning
Remove orphaned identities when systems retire.
The Future: Trust in Automation
As AI, RPA, and autonomous systems grow, so will the complexity of machine identities. Organizations must ensure:
Why Partner with Bridgesoft?
Our identity centric security solutions are designed for modern enterprises, providing:
Machine identities are the backbone of automation secure them with Bridgesoft.
In recent years, the strategic role of Identity and Access Management (IAM) has undergone a dramatic transformation. Once viewed primarily as a back-office function confined to IT departments, identity is now central to the success of digital business initiatives, cybersecurity strategies, and regulatory compliance efforts.
This evolution has been driven by a convergence of forces: the shift to cloud-based infrastructure, the rise of hybrid work, the increasing complexity of access environments, and the growing sophistication of cyber threats. As organizations expand their digital footprint, the challenge of managing who has access to what and ensuring that access is appropriate, secure, and accountable has never been more urgent.
Identity has become the control plane for modern enterprises. It is the common thread connecting employees, contractors, third-party partners, and machine identities to the systems and data they need. And because every interaction starts with identity, it is now a primary target for adversaries. Compromised credentials are consistently cited as a leading cause of breaches across industries.
Organizations are no longer operating within traditional network perimeters. The rapid adoption of SaaS applications, remote work environments, and third-party integrations has pushed access outside the enterprise boundary. As a result, identity is now the last line of defence. Effective identity governance enables real-time visibility and control over access, mitigating the risk of lateral movement in the event of a breach and limiting exposure to sensitive data.
Modern identity programs go far beyond provisioning accounts and managing passwords. When aligned with broader business objectives, IAM can accelerate user onboarding, streamline compliance reporting, reduce operational overhead, and improve the user experience.
For example, by integrating identity systems with HR platforms, access can be automatically assigned and revoked as users join, move, or leave the organization. This reduces manual effort and human error, while ensuring users have the right access at the right time. Additionally, advanced capabilities like identity analytics and AI-powered anomaly detection enable security teams to proactively respond to access-related risks helping to shift identity from a reactive function to a strategic advantage.
A successful identity program requires coordination across multiple stakeholders security teams, IT operations, HR, compliance, and business unit leaders. Yet in many organizations, these functions operate in silos. IAM implementations often stall due to unclear ownership, conflicting priorities, or poor communication between departments.
Establishing a cross-functional identity governance model can help bridge these gaps. This means bringing stakeholders together to define common objectives, clarify roles and responsibilities, and establish metrics that align with broader business goals. With the right collaboration, IAM can become a unifying force rather than a point of friction enabling secure
As digital ecosystems grow more complex and interconnected, identity will continue to play a defining role in shaping enterprise risk and opportunity. Organizations that recognize IAM as a strategic asset and invest in building mature, outcome-driven identity programs will be better positioned to thrive in a fast-changing landscape.
Ignoring identity’s expanding role comes at a cost. Whether it’s through compliance gaps, delayed onboarding, or increased exposure to threats, treating IAM as a low-priority technical project is a missed opportunity. The organizations that succeed will be those that elevate identity to the level of strategic infrastructure on par with cloud, data, and cybersecurity.
Partner with Bridgesoft to Transform Identity into Opportunity
At Bridgesoft, we understand that identity is more than just a technical control, it's the foundation of trust, security, and agility in today’s digital enterprise. With deep expertise in IAM strategy, deployment, and governance across industries, we help organizations turn identity challenges into business enablers. Whether you’re modernizing your access architecture, achieving compliance, or preparing for the next phase of digital growth, Bridgesoft delivers customized, scalable solutions to meet your unique needs.
We've all been there, right? That frustrating dance between getting our work done and navigating the labyrinth of cybersecurity. Organizations are rightly strengthening their digital defenses, but it often feels like every new security measure another authentication step, an extra access form, a policy update – adds friction. While these steps are designed to boost security, they can also leave us feeling frustrated and slow down our productivity.
But here's the thing: this trade-off is no longer acceptable. In today's hyper-digital world, how we interact online defines everything, from customer engagement to employee productivity. That means user experience isn't just a nice-to-have; it's a fundamental security requirement. For identity and security leaders, finding that sweet spot between robust protection and effortless usability has become one of the most pressing challenges.
Security That Empowers, Not Impedes
Think about it: when security controls become a roadblock to getting work done, what happens? People find workarounds. They might reuse passwords, share credentials, or even squirrel away sensitive information in less-than-secure spots. These aren't acts of negligence; they're often cries for help, signals that our security strategy isn't quite in sync with how people operate.
This is where modern Identity and Access Management (IAM) solutions truly shine. They're evolving to match the pace and reality of how we work. Imagine adaptive authentication that understands your context, single sign-on (SSO) that eliminates repetitive logins, or even a future where passwords are a thing of the past. These aren't just buzzwords; they're practical ways to enhance security without forcing users to jump through unnecessary hoops. When security feels seamless, people embrace it, and in turn, risk naturally decreases.
Weaving Design Thinking into Identity Programs
User-centric design isn't just for marketing and product teams anymore; it's a powerful tool for identity strategy. By embracing principles like empathy, rapid prototyping, and continuous iteration, identity leaders can craft workflows and access controls that genuinely reflect user needs.
Take, for instance, designing a new role-based access request system. Instead of simply building it and expecting people to adapt, imagine starting with conversations across different business units. What do users really need access to? How often do those needs shift? And crucially, by building in feedback loops, identity teams can constantly refine these systems based on real-world usage. The outcome? A more intuitive experience for users and a more efficient system for IT and security teams to manage. It's a win-win.
Building Trust Through Openness
Security shouldn't feel like something imposed on users; it should be something they understand and trust. When people are informed about why certain controls are in place, and when they have clear, easy-to-navigate options for requesting access or reporting issues, they're far more likely to embrace and adhere to security protocols.
Providing self-service capabilities, transparent access policies, and real-time visibility into permissions cultivates a culture of trust across the organization. It transforms security from a stern gatekeeper into a collaborative partner one that empowers employees to work confidently, knowing they're protected.
The Bridgesoft Perspective: Security as an Enabler
Ultimately, the most successful identity programs are those built with people at their core. When user experience and security are viewed as complementary forces rather than opposing ones, organizations can create digital environments that are both robustly secure and truly supportive.
At Bridgesoft, we believe that IAM shouldn't force anyone to choose between security and speed. With the right tools, the right mindset, and the right processes, it's not only possible to deliver both, but to elevate the identity function into a genuine driver of business value. We empower organizations to build secure, seamless digital experiences that foster productivity and trust, because we understand that the human element is at the heart of every successful cybersecurity strategy.
Identity is no longer a background function. It’s a strategic driver of security, user experience, digital transformation, and even competitive advantage. As cloud adoption, remote work, and regulatory demands reshape the enterprise, identity has emerged as the control plane for the modern organization.
But this landscape is far from static. The next evolution of identity is already underway, shaped by emerging technologies, evolving threats, and rising expectations from users and regulators alike.
Understanding what’s next is essential for IAM leaders, CISOs, and IT decision-makers looking to future-proof their programs. This post explores the key trends that will define the future of identity and what organizations can do now to prepare.
Traditional identity models rely on centralized providers directories, identity platforms, or federated systems to verify and store credentials. But with increasing concerns about data privacy, portability, and control, decentralized identity (DID) is gaining traction.
In a decentralized identity ecosystem, individuals manage their own credentials using digital wallets. Verifiable credentials such as proof of employment, age, or certifications are issued by trusted authorities and presented only when needed. No centralized store, no password reuse, and no unnecessary collection of PII.
This model holds enormous promise:
However, adoption will take time. Standards like W3C’s DID and Verifiable Credentials are still maturing, and interoperability challenges remain. But make no mistake: user-centric identity is coming, and it will shift how organizations think about onboarding, access, and trust.
Artificial Intelligence is rapidly transforming cybersecurity and identity is no exception. On one side, IAM platforms are integrating AI to drive efficiency and enhance risk detection. On the other, identity systems are becoming core data sources for AI models.
AI-powered IAM brings benefits such as:
But there’s also a growing recognition that identity data itself is a critical input to AI governance. As enterprises deploy AI models, identity will help answer questions like: Who trained this model? Who can modify it? Who is responsible for its outputs?
Going forward, expect to see tighter integration between identity governance and AI governance especially in regulated industries where explainability and accountability are key.
Passwords have long been the weakest link in security. They’re reused, forgotten, phished, and frequently compromised. Organizations have responded with MFA, but even that’s not immune to sophisticated attacks like MFA fatigue and phishing kits that intercept codes.
Now, a true shift is underway: passwordless authentication is moving from aspiration to standard.
Technologies like FIDO2/WebAuthn, biometric authentication, and device-based identity are allowing organizations to eliminate passwords altogether replacing them with cryptographic credentials stored on user devices.
This improves:
Adoption is growing, especially in customer-facing apps and modern workforce platforms. Within the next few years, passwordless will likely become the norm and organizations still reliant on passwords will find themselves increasingly exposed.
As discussed in earlier posts, non-human identities including APIs, service accounts, bots, and containers now outnumber human users in many environments. Yet governance for these identities is still catching up.
In the future, expect to see:
Organizations that delay governance in this area are inviting risk. Just as we’ve matured our processes around joiners, movers, and leavers for people, we must now do the same for code.
As threat actors increasingly target identities rather than infrastructure, Identity Threat Detection and Response (ITDR) is emerging as a key pillar of modern security.
ITDR involves detecting, investigating, and responding to identity-related threats such as privilege escalation, lateral movement via service accounts, and misuse of legitimate credentials.
Expect to see:
Identity isn’t just about provisioning anymore. It’s about active defense and ITDR is how organizations will stay ahead of adversaries.
Historically, compliance was a periodic effort to prepare for the audit, run the reports, close the gaps. But as regulations evolve and expectations shift, compliance is moving toward real-time, continuous assurance.
This requires:
IAM platforms will need to evolve from systems of record to systems of accountability, capable of proving compliance on demand and adapting to new rules as they emerge.
The future of identity is not a single destination it’s a constantly evolving landscape shaped by technology, threat actors, business needs, and user expectations. As identity becomes more decentralized, intelligent, and embedded into everything we do, the organizations that thrive will be those that embrace change, invest in innovation, and treat identity as strategic infrastructure.
